eSigning with PIV and CAC smart cards in U.S. government agencies
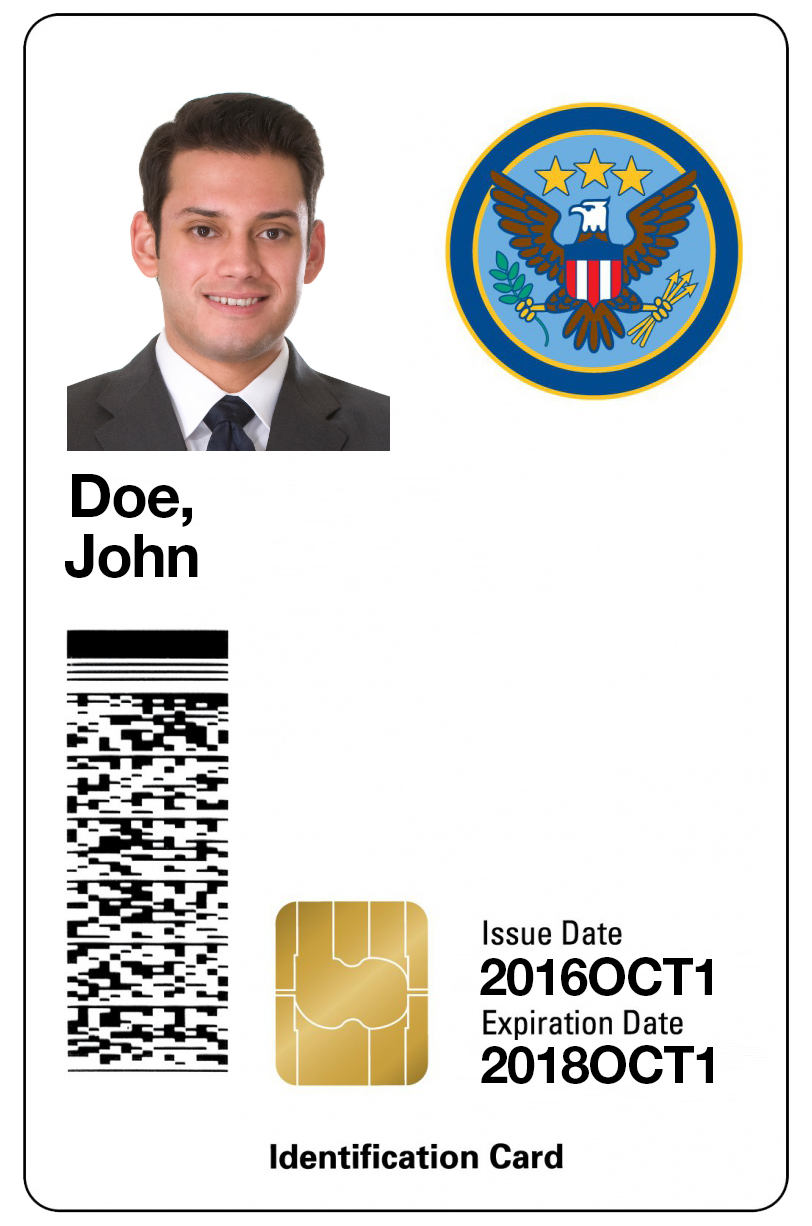
When it comes to privacy and security of data, US government agencies use a Common Access Card (CAC) or a Personal Identity Verification Card (PIV) to manage access and authenticate government employees in the active directory. Roughly the size of a credit card, CAC and PIV smart cards store data such as digital certificates, biometric information, photo, expiration date, government agency and department, and other information that identifies the smart card holder. When authenticating or accessing information, the government agency employee inserts their smart card in a card reader to securely authenticate themselves.
History of CAC and PIV Smart Cards
In the late 1990’s, Congress directed the Secretary of Defense to implement an Identity Management System for the Department of Defense (DoD) that would increase security and efficiency. A set of credentials was created whereby identity can easily be managed across all federal government agencies which led to the creation of the Common Access Card (CAC). The CAC Card quickly became the standard and was issued to Active Duty Military, DoD and contractors to the Government. The CAC then transitioned from a basic card to one leveraging Public Key Infrastructure (PKI), based on cryptography.
Around 2006, the Homeland Security Presidential Elective 12 (HSPD-12) was introduced, which provides guidance on how to implement the newly introduced Federal Information Processing Standard 201 (FIPS-201). Basically, this standard takes Identity Management to a new level, including provisions for cashless transaction.
This new standard is known today as a Personal Identity Verification Card (PIV) or PIV authentication certificate (PIV-auth certificate). While PIV authentication presents some challenges to use (i.e.: using a card reader attached to every device you use; being required to activate PIV credentials beforehand), initiatives are underway to implement Soft Certificates, allowing for Derived Credentials. The Derived Credentials of the ID card can be stored directly into a government issued device such as smartphones or tablets, eliminating the need to use the physical card.
E-Signing with CAC and PIV Smart Cards
OneSpan Sign is used by government organizations whose employees and contractors routinely e-sign forms and documents using a digital certificate stored on CAC or PIV smart cards. This provides strong two-factor authentication with something the user knows (the PIN for their cards), and something the user has (the card).
Government agencies are leveraging issued CAC and PIV smart cards to e-sign documents for many use cases such as e-contracting, procurement, Finance, and HR, just to name a few. As an example, USDA employees e-sign documents daily by simply inserting their LincPass smartcard into a slot on their keyboard or laptop. They then enter a 6-8 digit PIN. Once successfully authenticated, they can apply their e-signature to documents.
Here’s how access control with smart cards works:
E-Signing with CAC and PIV Smart Cards can be completed by following these easy steps:
- Insert your CAC or a PIV card into your laptop, mobile device, or smart card reader
- Logon and access the document that requires your e-signature within OneSpan Sign
- When the document is displayed and ready to be signed, click the signature block then confirm your signature.
- The Certificate Selection dialog box appears. Select the appropriate certificate from the list. If prompted, enter a personal identification number (PIN) code associated to the selected security certificate. Once the PIN is confirmed, OneSpan Sign generates a hash of your information at the time of signing (name, date, time, IP address, certificate used to sign the document), along with a unique hash of the document itself. The result is a secure, tamper-sealed e-signed PDF with a detailed audit trail embedded directly into the document.
For example, the process used by the United States Department of Agriculture (USDA) follows this model. USDA employees e-sign documents by inserting their LincPass smartcard into a slot on their keyboard or laptop. Once successfully authenticated, they can apply their e-signature to documents for full non-repudiation.
Check out the video tutorial below to see how you can easily e-sign documents with smart cards in OneSpan Sign.