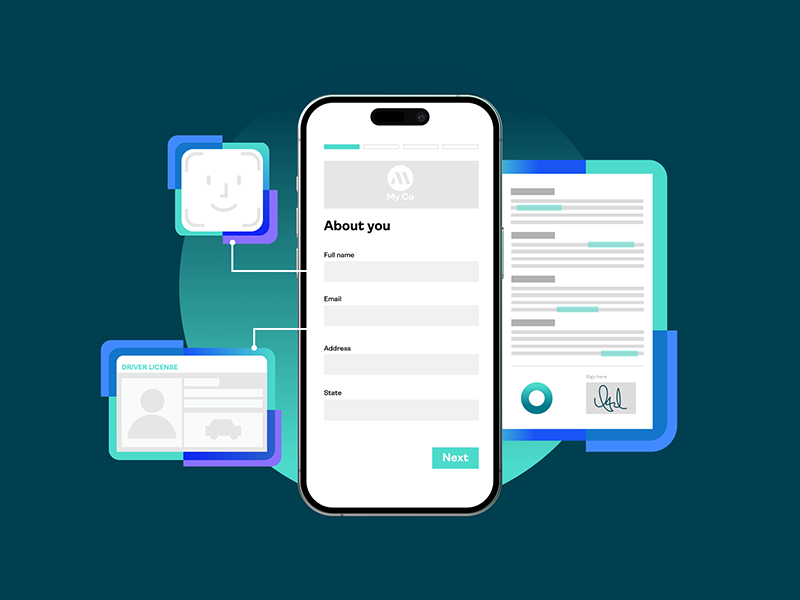
Fast, secure, digital: Rethinking digital forms and agreements
Businesses are converting PDF forms into mobile-friendly, digital forms. Data capture fuels digital...

How to streamline legal document management with eSignatures
Discover the future of legal document management – seamless, digital, and transparent solutions for...

2024: The age of a workforce free from passwords
Now that digitalization has become ubiquitous and remote work is here to stay, organizations worldwide...

NIS2 Directive (part 1): What is new in NIS2 and who does it apply to?
In the EU, the NIS2 Directive mandates strong authentication for employees in certain industries....

NIS2 Directive (part 2): Strong authentication requirements for employees in critical industry sectors in Europe
In the EU, the NIS2 Directive mandates strong authentication for employees in certain industries....

Top banking regulations & security compliance requirements 2024
Explore essential banking regulations and security compliance, including cybersecurity, digital identity...

Why hardware devices should be a key ingredient of banks’ strong customer authentication strategy
Find out why hardware authentication devices represent an important security component of online banking...

Mentorship for women at OneSpan
How leaders at OneSpan are doing their part to close the gender gap in the technology industry through...
